- Power BI forums
- Updates
- News & Announcements
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Power Platform Integration - Better Together!
- Power Platform Integrations (Read-only)
- Power Platform and Dynamics 365 Integrations (Read-only)
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Events
- Ideas
- Custom Visuals Ideas
- Issues
- Issues
- Events
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Register now to learn Fabric in free live sessions led by the best Microsoft experts. From Apr 16 to May 9, in English and Spanish.
- Power BI forums
- Forums
- Get Help with Power BI
- Developer
- Native App for data push with auto login
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Native App for data push with auto login
Hello everyone,
I'm building a console application using Visual Studio 2017 in order to push data into a Power BI dataset. I followed this guide:
Everithing it's working fine but i need to get a token with a non-interactively authentication to Azure AD. In a few words, without GUI on which user select his username. In internet I can't find anything that explains how to do that with a Native App. I only found how to do that with App Web/API using the clientID and secretID, but with Native App I haven't any secretID. Moreover with a App Web/API I got an Unauthorized (401) when I try to create a DataSet.
Someone could please help me to find a solution? Keep in mind that I never want the login screen to appear, so the solution of token stored in the cache is useless for me.
I appreciate any kind of help. Thanks,
amatteo90
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @amatteo90,
Could you please mark the proper answers as solutions?
Best Regards,
Dale
If this post helps, then please consider Accept it as the solution to help the other members find it more quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @amatteo90,
How did you try to get the token? Since there are many methods, the process of authentication depends on your code. Please refer to the Python script below, which use a username and a password to get the access token.
We can get the token for both Native App and Web App unless the AAD requires two-factor authentication.
Reference: azure-activedirectory-library-for-python and active-directory/develop/v1-oauth2-implicit-grant-flow.
# adal is azure-activedirectory-library-for-python. install it first.
from adal import AuthenticationContext
# get access token implictly with username and password.
def get_token():
client_id = "a30***1ae1dcde27e"
resource_uri = "https://analysis.windows.net/powerbi/api"
user_name = "d**.com"
user_password = "password"
auth_context = AuthenticationContext("https://login.microsoftonline.com/your_tenant_name")
token_response = auth_context.acquire_token_with_username_password(resource_uri, user_name, user_password, client_id)
token = "Bearer " + token_response["accessToken"]
return token
Best Regards,
Dale
If this post helps, then please consider Accept it as the solution to help the other members find it more quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I'm trying to do the same thing:
You can't generate an app key when you have selected Native app type. You have to select Web/API.
This sample shows you how to use the app secret:
https://github.com/azure-samples/active-directory-dotnet-daemon
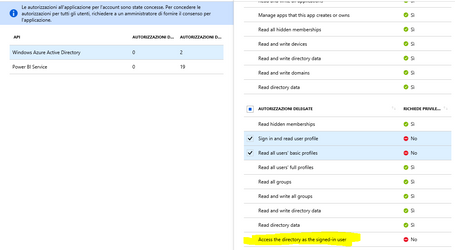
I get 401 errors when I try to call the REST API though. This is even though my app has been granted permissions by a Global Admin.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
Thanks for the answer, By using a Web App I haven't any problem to perform a login with no GUI for authentication. However I got a 401 error when I try to call the REST API like you.
For Power BI Service I've granted any king of delegate authorizations that requires no administrator privileges. However I've a problem to grant the authorization "Access the directory as the signed-in user" even if doesn't require administrator privileges. Maybe is this the problem?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not sure the Delegated permissions are used at all when authenticating using an app key/service principal...
Types of permissions
Azure AD defines two kinds of permissions:
- Delegated permissions - Are used by apps that have a signed-in user present. For these apps, either the user or an administrator consents to the permissions that the app requests and the app is delegated permission to act as the signed-in user when making calls to an API. Depending on the API, the user may not be able to consent to the API directly and would instead require an administrator to provide "admin consent".
- Application permissions - Are used by apps that run without a signed-in user present; for example, apps that run as background services or daemons. Application permissions can only be consented by an administrator because they are typically powerful and allow access to data across user-boundaries, or data that would otherwise be restricted to administrators.
Helpful resources

Microsoft Fabric Learn Together
Covering the world! 9:00-10:30 AM Sydney, 4:00-5:30 PM CET (Paris/Berlin), 7:00-8:30 PM Mexico City

Power BI Monthly Update - April 2024
Check out the April 2024 Power BI update to learn about new features.

| User | Count |
|---|---|
| 12 | |
| 2 | |
| 2 | |
| 1 | |
| 1 |
| User | Count |
|---|---|
| 20 | |
| 3 | |
| 2 | |
| 2 | |
| 2 |