- Power BI forums
- Updates
- News & Announcements
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Power Platform Integration - Better Together!
- Power Platform Integrations (Read-only)
- Power Platform and Dynamics 365 Integrations (Read-only)
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Events
- Ideas
- Custom Visuals Ideas
- Issues
- Issues
- Events
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Register now to learn Fabric in free live sessions led by the best Microsoft experts. From Apr 16 to May 9, in English and Spanish.
- Power BI forums
- Forums
- Get Help with Power BI
- Developer
- Re: Authorization fails trying to invoke PowerBI R...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Authorization fails trying to invoke PowerBI Rest API from C# Function App
I am trying to implement a C# Azure Function App to use the PowerBI Rest API to extract information about workspaces etc in our tenant.
As a starting point I used Jeff Pries's excellent blog post:
Initially I implemented this as a standalone local app and it worked fine. So I know that I have setup my App Registration correctly in the Azure AD and I know that I can successfully authorize non-interactively with saved User/Password credentials and obtain a list of PowerBI workspaces on our tenant.
However, when I came to implement this in an Azure Function App I found that the option to use User/Password isn't available, so instead am trying using a ClientSecret to authenticate, but cannot get it to work.
I am using AcquireTokenAsync method to get the auth token:
authResult = await authContext.AcquireTokenAsync(ResourceURL, clientCredential).ConfigureAwait(false);
I know I am using the correct client secret because if I deliberately use the wrong one I get an "Invalid client secret is provided" exception.
I then CreateAuthorizationHeader method to create the authorization header
authToken = authResult.Result.CreateAuthorizationHeader();
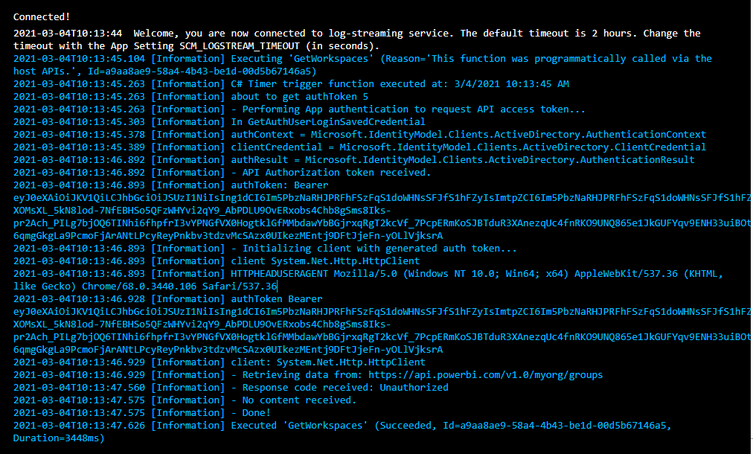
You can see from the console screenshot below that this all appears to work fine. I end up with a sound looking bearer token:
Then I create an HTTPClient and set the auth token in the Authorization header:
client = new HttpClient();
client.DefaultRequestHeaders.UserAgent.ParseAdd(HTTPHEADUSERAGENT);
client.DefaultRequestHeaders.Add("Authorization", authToken);
Finally, I try to use the client to call the PowerBI API:
string serviceURL ="https://api.powerbi.com/v1.0/myorg/groups";
response = client.GetAsync(serviceURL).Result;
Every time I get response code: Unauthorized.
What am I doing wrong?
The ResourceURL I am using to acqure the token is: "https://analysis.windows.net/powerbi/api".
I have tried using different versions of the Microsoft.IdentityModel.Clients.ActiveDirectory. I tried using the latest v5.2.8, but I have also seen posts which suggest the problem could be solved by using v3.19.8. But neither makes any difference.
The AuthorityURL I am using to get the auth context for v3.19.8 is: "https://login.windows.net/common/oauth2/authorize".
The AuthorityURL I am using to get the auth context for v5.2.8 was: "https://login.microsoftonline.com/common". I also tried using URLs that include our tenant id.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
HI @joolzfawcett,
Maybe you can try to refer to the following document sample codes to replace the get token parts and test to confirm if this token works on your side.
Step 2: Get an authentication access token
Please also take a look at the best practice of azure function if it helps:
Best practices for performance and reliability of Azure Functions
Regards,
Xiaoxin Sheng
If this post helps, please consider accept as solution to help other members find it more quickly.
Helpful resources

Microsoft Fabric Learn Together
Covering the world! 9:00-10:30 AM Sydney, 4:00-5:30 PM CET (Paris/Berlin), 7:00-8:30 PM Mexico City

Power BI Monthly Update - April 2024
Check out the April 2024 Power BI update to learn about new features.

| User | Count |
|---|---|
| 13 | |
| 2 | |
| 2 | |
| 1 | |
| 1 |