- Power BI forums
- Updates
- News & Announcements
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Power Platform Integration - Better Together!
- Power Platform Integrations (Read-only)
- Power Platform and Dynamics 365 Integrations (Read-only)
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Events
- Ideas
- Custom Visuals Ideas
- Issues
- Issues
- Events
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Register now to learn Fabric in free live sessions led by the best Microsoft experts. From Apr 16 to May 9, in English and Spanish.
- Power BI forums
- Forums
- Get Help with Power BI
- Desktop
- Microsoft Graph: Access to the resource is forbidd...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
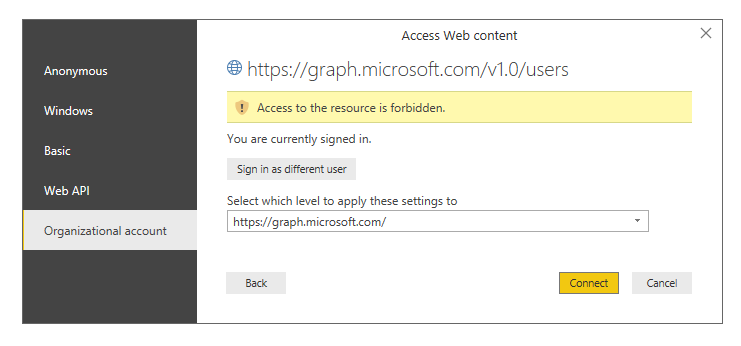
Microsoft Graph: Access to the resource is forbidden.
I'm wondering if there have been potentially any changes to Microsoft Graph's ability to be queried via the user login auth flow.
I've got clients using Microsoft Graph in their Power BI reports, and it's fairly simple to use that data. You can use an OData feed or the Web connector, and you authenticate with an Organizational Account. These same reports have been using Graph with no issue for quite some time, and this is occuring across multiple AAD tenancies, not just us or one particular client.
For some reason, now all attempts to use Graph end up in a 403/forbidden response from Power BI. I can log into the Graph Explorer and successfully pull the data there. An example endpoint is "https://graph.microsoft.com/v1.0/users". I'm absolutely certain I have all required permissions to view a user list.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Anonymous,
Updates of this issue:
We do not support connecting to Graph. Because of various auth challenges, generic OData connectivity does not work.
Users should vote for a dedicated Graph connector on UserVoice to register their interest.
Best Regards,
Dale
If this post helps, then please consider Accept it as the solution to help the other members find it more quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We need to vote to show our interest in a feature we were already using until it was abruptly turned off?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@v-jiascu-msft, I think what we're curious about is why it worked for so long, and suddenly now it doesn't. Was this a recent change on the evening of May 31st in relation to GDPR initiatives?
In this situation, we had access to a wealth of data from our AAD tenancies that was very useful in RLS and other scenarios, and suddenly it stopped working (with a basic OAuth flow/signing in with delgated scope). You end up with consumers and consultants building dependencies on these integrations, and then it changes without warning.
While I'm sure you can't revert whatever these changes were, I would love to have a more grounded conversation with our clients as to why a working solution is suddenly broken without any explanation from Microsoft. I was able to make a new solution leveraging an actual Azure AD registered application with Graph permissions, but this caused scope change and user interruptions in the meantime.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Anonymous,
Thanks for the feedback. I would suggest you follow this thread or create a support ticket here.
Best Regards,
Dale
If this post helps, then please consider Accept it as the solution to help the other members find it more quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Anonymous,
It seems the same issue with this thread that has been reported.
Best Regards,
Dale
If this post helps, then please consider Accept it as the solution to help the other members find it more quickly.
Helpful resources

Microsoft Fabric Learn Together
Covering the world! 9:00-10:30 AM Sydney, 4:00-5:30 PM CET (Paris/Berlin), 7:00-8:30 PM Mexico City

Power BI Monthly Update - April 2024
Check out the April 2024 Power BI update to learn about new features.

| User | Count |
|---|---|
| 116 | |
| 104 | |
| 77 | |
| 71 | |
| 50 |
| User | Count |
|---|---|
| 146 | |
| 107 | |
| 106 | |
| 89 | |
| 65 |