- Power BI forums
- Updates
- News & Announcements
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Power Platform Integration - Better Together!
- Power Platform Integrations (Read-only)
- Power Platform and Dynamics 365 Integrations (Read-only)
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Events
- Ideas
- Custom Visuals Ideas
- Issues
- Issues
- Events
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Register now to learn Fabric in free live sessions led by the best Microsoft experts. From Apr 16 to May 9, in English and Spanish.
- Power BI forums
- Forums
- Get Help with Power BI
- Desktop
- Allowing User Higher Security
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Allowing User Higher Security
Community,
I've got our security roles for a report set up like so:
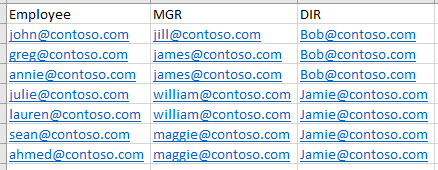
We have a table with employees, their managers, and their directors. A sample of what this table looks like is included below. I've got security set up with this formula:
OR(USERPRINCIPALNAME() = 'Table'[Employee]
, OR(USERPRINCIPALNAME() = 'Table'[MGR]
, USERPRINCIPALNAME() = 'Table'[DIR]
)
)
This table is connected to others by the IDs of employees. It appears to correctly work for each level in the hierarchy; directors can only see people under them, managers can only see the people under them, employees in this role would only be able to see activity related to themselves.
However, recently we discussed this with some the end-using directors, and they said that they would like to allow their employees to see the activities of others on their teams; effectively giving them the same access as their managers.
MY QUESTION is, if security is based off of USERPRICIPALNAME, how can I make a new role that will basically ignore that and allow an employee to view what their manager views?
For instance, if I am Julie, then I should also be able to see Lauren's activities because we are both on William's team.
There may be some compliacations to this, but those should be subjects for other threads. Thank you for your suggestions and assistance.
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can use the LOOKUPVALUE formula to get around using userprincipalname() as the basis for your RLS by making another field of the table the key off of which you're basing your RLS.
In this case, you would set up a new Role with RLS as:
'Table'[MGR] = LOOKUPVALUE('Table'[MGR], 'Table'[Employee], USERPRINCIPALNAME())
In other words, "give access to the records where the manager is that matching the manager of the user."
This would give an employee the same access as their managers.
You can apply this method to all kinds of things.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can use the LOOKUPVALUE formula to get around using userprincipalname() as the basis for your RLS by making another field of the table the key off of which you're basing your RLS.
In this case, you would set up a new Role with RLS as:
'Table'[MGR] = LOOKUPVALUE('Table'[MGR], 'Table'[Employee], USERPRINCIPALNAME())
In other words, "give access to the records where the manager is that matching the manager of the user."
This would give an employee the same access as their managers.
You can apply this method to all kinds of things.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @jengwt,
=> recently we discussed this with some the end-using directors, and they said that they would like to allow their employees to see the activities of others on their teams; effectively giving them the same access as their managers.
You can set Dynamic Row Level Security with Organizational Hierarchy in Power BI. However for the lowest level, the RLS just works for the current given user. It also means even one other user has the same level with the current given user, it is still unable to display data of the other user. So I'm afraid your requirement cannot be achieved.
By the way, as you said that the new RLS is just same as the managers. Why don't you just use the manager level RLS?
Thanks,
Xi Jin.
Helpful resources

Microsoft Fabric Learn Together
Covering the world! 9:00-10:30 AM Sydney, 4:00-5:30 PM CET (Paris/Berlin), 7:00-8:30 PM Mexico City

Power BI Monthly Update - April 2024
Check out the April 2024 Power BI update to learn about new features.

| User | Count |
|---|---|
| 111 | |
| 100 | |
| 80 | |
| 64 | |
| 58 |
| User | Count |
|---|---|
| 148 | |
| 111 | |
| 93 | |
| 84 | |
| 66 |